Invalid Maximum Validity Date Detected During Qualys Scan - QID: 38685 (KBA7771)
KBA
KBA# 7771
Issue
Qualys Scan may report vulnerability SSL Certificate - Invalid Maximum Validity Date Detected when scanning a Delphix Engine. This is categorized under QID 38685.
Applicable Delphix Versions
- Click here to view the versions of the Delphix engine to which this article applies
-
Major Release All Sub Releases 6.0 6.0.0.0, 6.0.1.0, 6.0.1.1, 6.0.2.0, 6.0.2.1, 6.0.3.0, 6.0.3.1, 6.0.4.0, 6.0.4.1, 6.0.4.2, 6.0.5.0, 6.0.6.0, 6.0.6.1, 6.0.7.0, 6.0.8.0, 6.0.8.1 5.3
5.3.0.0, 5.3.0.1, 5.3.0.2, 5.3.0.3, 5.3.1.0, 5.3.1.1, 5.3.1.2, 5.3.2.0, 5.3.3.0, 5.3.3.1, 5.3.4.0, 5.3.5.0, 5.3.6.0, 5.3.7.0, 5.3.7.1, 5.3.8.0, 5.3.8.1, 5.3.9.0 5.2
5.2.2.0, 5.2.2.1, 5.2.3.0, 5.2.4.0, 5.2.5.0, 5.2.5.1, 5.2.6.0, 5.2.6.1
5.1
5.1.0.0, 5.1.1.0, 5.1.2.0, 5.1.3.0, 5.1.4.0, 5.1.5.0, 5.1.5.1, 5.1.6.0, 5.1.7.0, 5.1.8.0, 5.1.8.1, 5.1.9.0, 5.1.10.0
5.0
5.0.1.0, 5.0.1.1, 5.0.2.0, 5.0.2.1, 5.0.2.2, 5.0.2.3, 5.0.3.0, 5.0.3.1, 5.0.4.0, 5.0.4.1, 5.0.5.0, 5.0.5.1, 5.0.5.2, 5.0.5.3, 5.0.5.4
Resolution
Recently, the Certificate Authority / Browser (CAB) Forum passed Ballot SC31, which recommends the allowable validity period for SSL certificates to be 398 days for certificates issued on or after Sept 1 2020 (398 days is one leap year, plus one month, plus a little extra buffer). As a result, participating Certificate Authorities as well as other vendors are now generally enforcing this new limit.
QID 38685 currently flags this vulnerability based on the Validity Period of the Engine SSL certificate; the "allowable" validity period is dependent on the date issued. From Qualys scan reports, the following details can be found under Threat field:
Subscriber Certificates issued on or after 1 September 2020 SHOULD NOT have a Validity Period greater than 397 days and MUST NOT have a Validity Period greater than 398 days. (13 months)
Subscriber Certificates issued after 1 March 2018, but prior to 1 September 2020, MUST NOT have a Validity Period greater than 825 days. (27 months)
Subscriber Certificates issued after 1 July 2016 but prior to 1 March 2018 MUST NOT have a Validity Period greater than 39 months.
SSL certificates have limited validity periods so that the certificate's holder identity information is re-authenticated more frequently.It is detected that maximum validity of certificate on the system is more than what is recommended.
This finding, although reported as a vulnerability, has no distinct exploit or CVE associated, and is a strong recommendation rather than a requirement.
The Delphix Engine self-signed certificates are automatically generated with a 4-year validity period. As a result, this Vulnerability will be reported for most default Engine configurations, or for those installations where the End Entity certificate replaced exceeds the validity period discussed above.
Although Delphix does not consider this to be a significant finding, the affected certificates can be replaced as desired through System Setup to comply with the recommended validity period. Details of this process are provided in Product Documentation:
https://cd.delphix.com/docs/latest/configuring-network-settings
Troubleshooting
When reviewing the Detailed Results portion of Qualys scan report, the certificate details can be located in the Information Gathered section, under SSL Certificate - Information. Here, the Certificate can be identified and correlated with the Engine configuration based on commonName and the Serial Number.
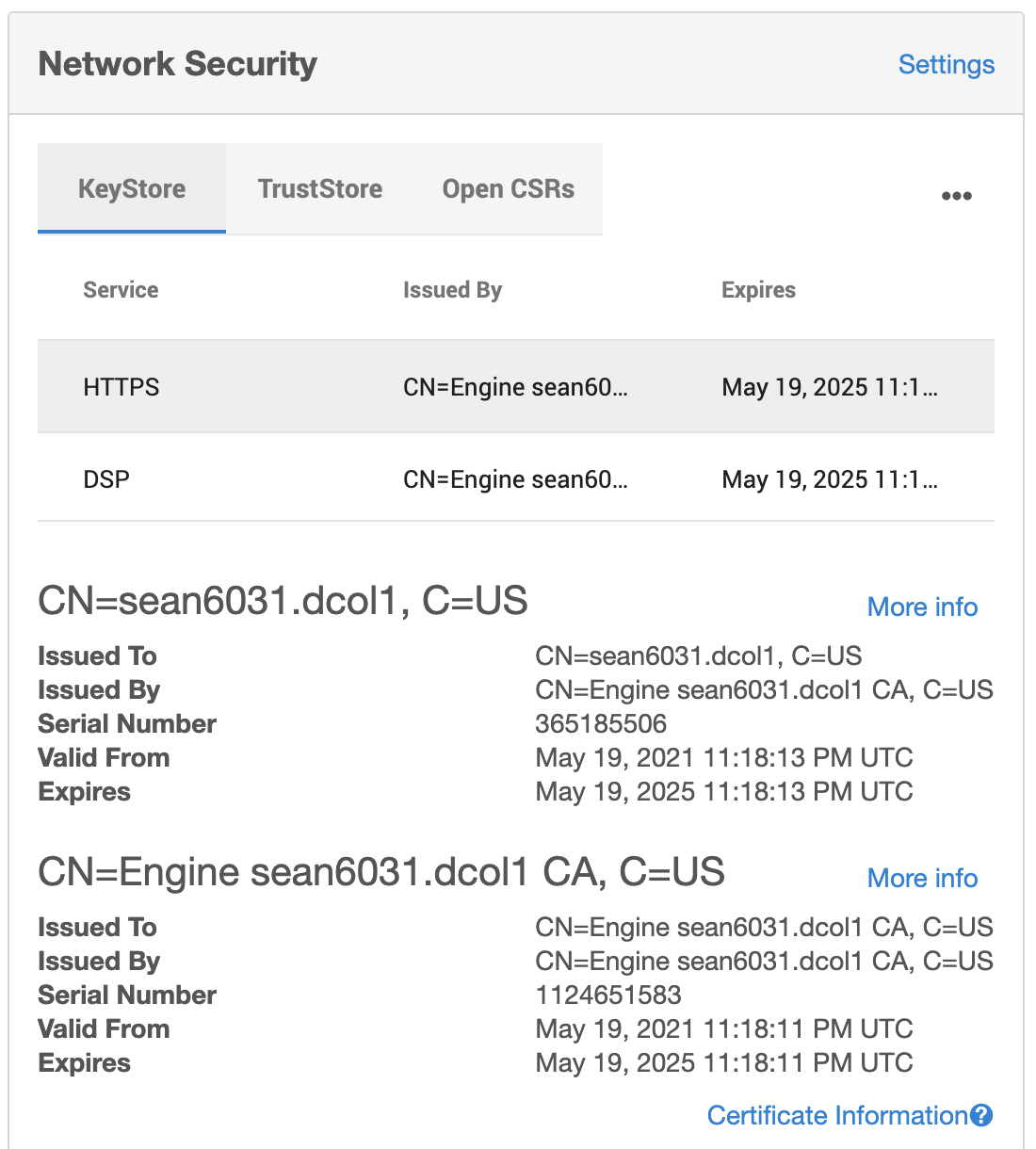
In the following example, we find the certificate details and serial number as follows, along with the validity period:
NAME VALUE (0)CERTIFICATE 0 (0)Version 3 (0x2) (0)Serial Number 365185506 (0x15c449e2) (0)Signature Algorithm sha256WithRSAEncryption (0)ISSUER NAME countryName US commonName CN=Engine sean6031.dcol1 CA (0)SUBJECT NAME countryName US commonName sean6031.dcol1 (0)Valid From May 19 11:18:13 2021 GMT (0)Valid Till. May 19 11:18:13 2025 GMT (0)Public Key Algorithm. rsaEncryption
The details of installed certificates in the Engine Keystore can then be reviewed under Network Security in System Setup application. In this example, we see the matching certificate serial number indicated:
This information can also be located in the sysadmin CLI under service/tls/endEntityCertificate
sean6031.dcol1> service tls endEntityCertificate
sean6031.dcol1 service tls endEntityCertificate> ls
Objects
NAME REFERENCE ENDENTITY.TYPE NOTAFTER
`END_ENTITY_CERTIFICATE-183A10B4A369C74A9A8C25D11E6534C81265729E/CN=sean6031.dcol1, C=US END_ENTITY_CERTIFICATE-183A10B4A369C74A9A8C25D11E6534C81265729E EndEntityHttps 2025-05-19T23:18:13.000Z
`END_ENTITY_CERTIFICATE-9E096B4E485C986FCB80AD04FEF056B4AA8FC3CD/CN=sean6031.dcol1, C=US END_ENTITY_CERTIFICATE-9E096B4E485C986FCB80AD04FEF056B4AA8FC3CD EndEntityDsp 2025-05-19T23:18:16.000Z
sean6031.dcol1 service tls endEntityCertificate> select END_ENTITY_CERTIFICATE-183A10B4A369C74A9A8C25D11E6534C81265729E
sean6031.dcol1 service tls endEntityCertificate '`END_ENTITY_CERTIFICATE-183A10B4A369C74A9A8C25D11E6534C81265729E/CN=sean6031.dcol1, C=US'> ls
Properties
type: EndEntityCertificate
name: `END_ENTITY_CERTIFICATE-183A10B4A369C74A9A8C25D11E6534C81265729E/CN=sean6031.dcol1, C=US
endEntity:
type: EndEntityHttps
isCertificateAuthority: false
issuedByDN: CN=Engine sean6031.dcol1 CA, C=US
issuer: CN=Engine sean6031.dcol1 CA, C=US
md5Fingerprint: 6251331f1ec8da0874a5e21ba382f052
notAfter: 2025-05-19T23:18:13.000Z
notBefore: 2021-05-19T23:18:13.000Z
reference: END_ENTITY_CERTIFICATE-183A10B4A369C74A9A8C25D11E6534C81265729E
serialNumber: 365185506
sha1Fingerprint: 183a10b4a369c74a9a8c25d11e6534c81265729e
Related Articles
The following articles may provide more information or related information to this article:
